
What Is Network Behavior Anomaly Detection? Definition, Importance, and Best Practices for 2022 - Spiceworks
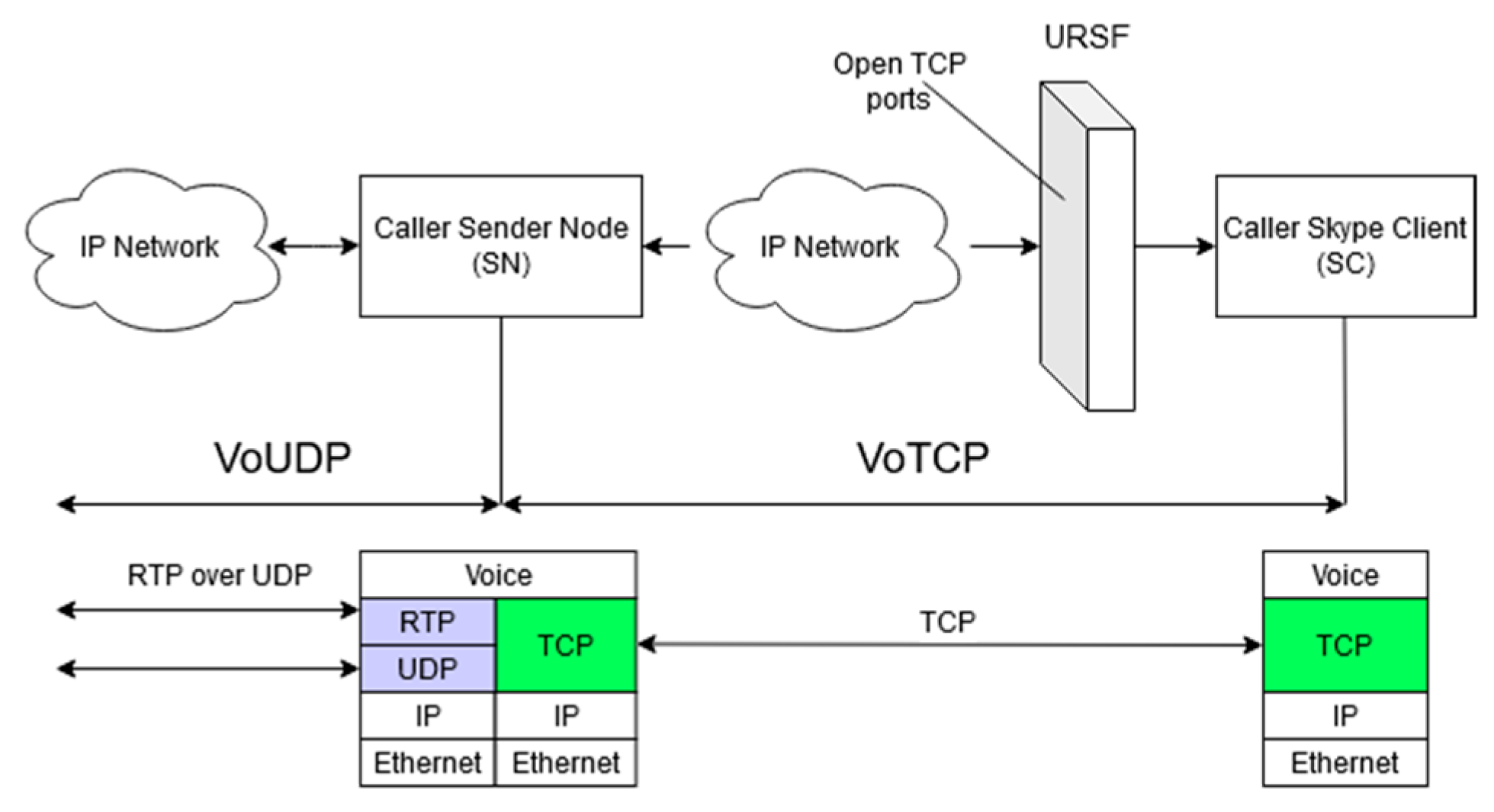
Network | Free Full-Text | Call Me Maybe: Using Dynamic Protocol Switching to Mitigate Denial-of-Service Attacks on VoIP Systems

Mission‐centric decision support in cybersecurity via Bayesian Privilege Attack Graph - Javorník - 2022 - Engineering Reports - Wiley Online Library
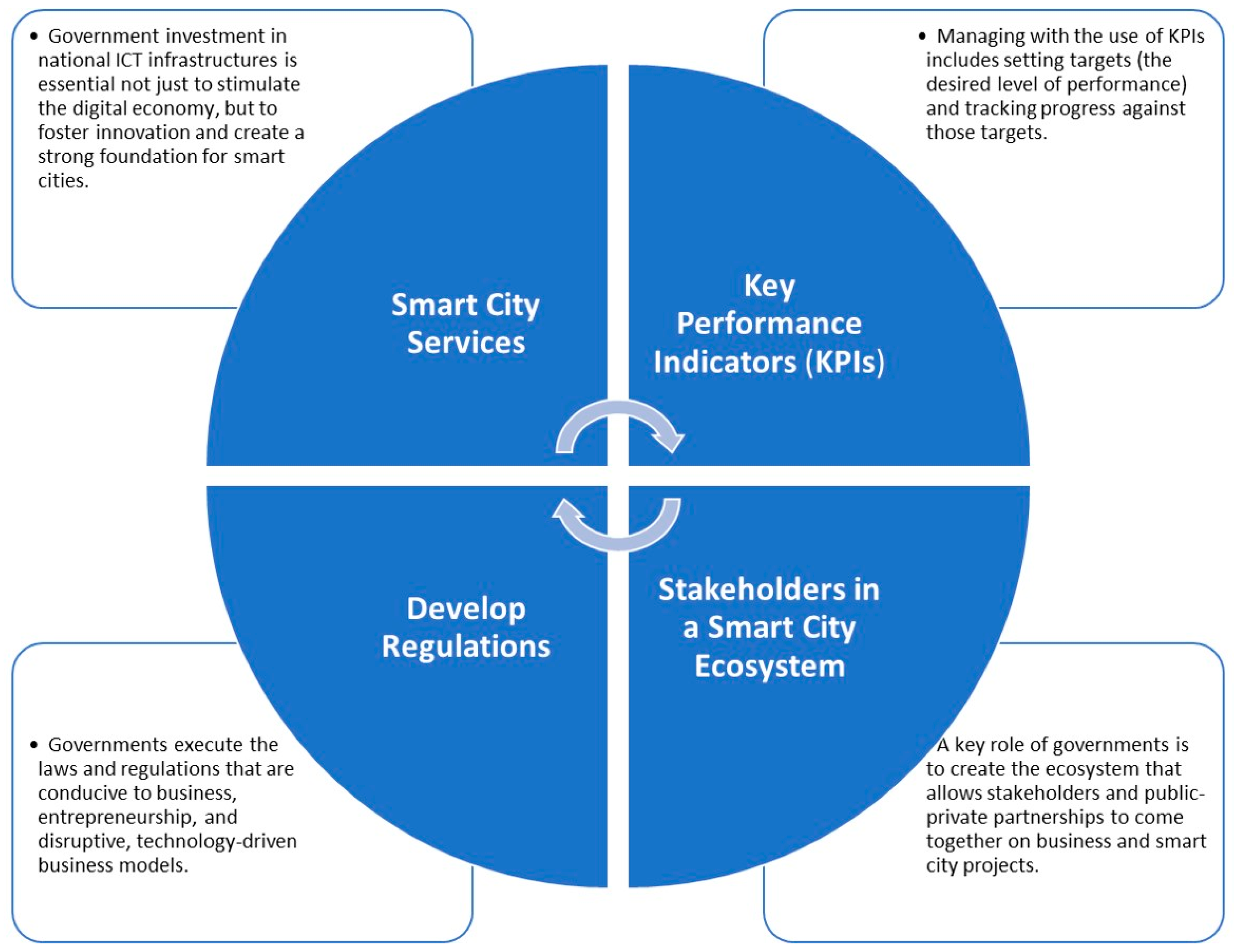
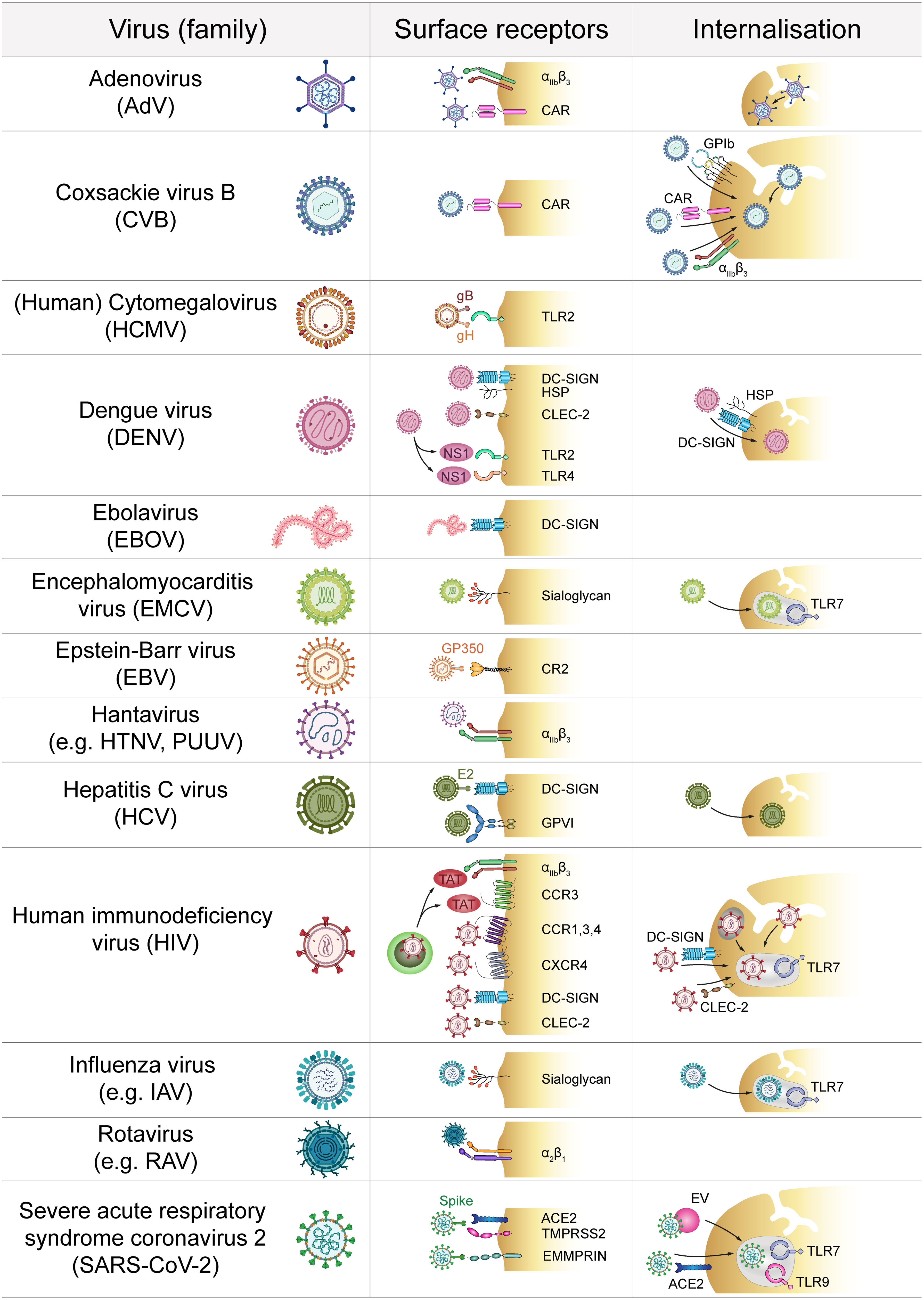
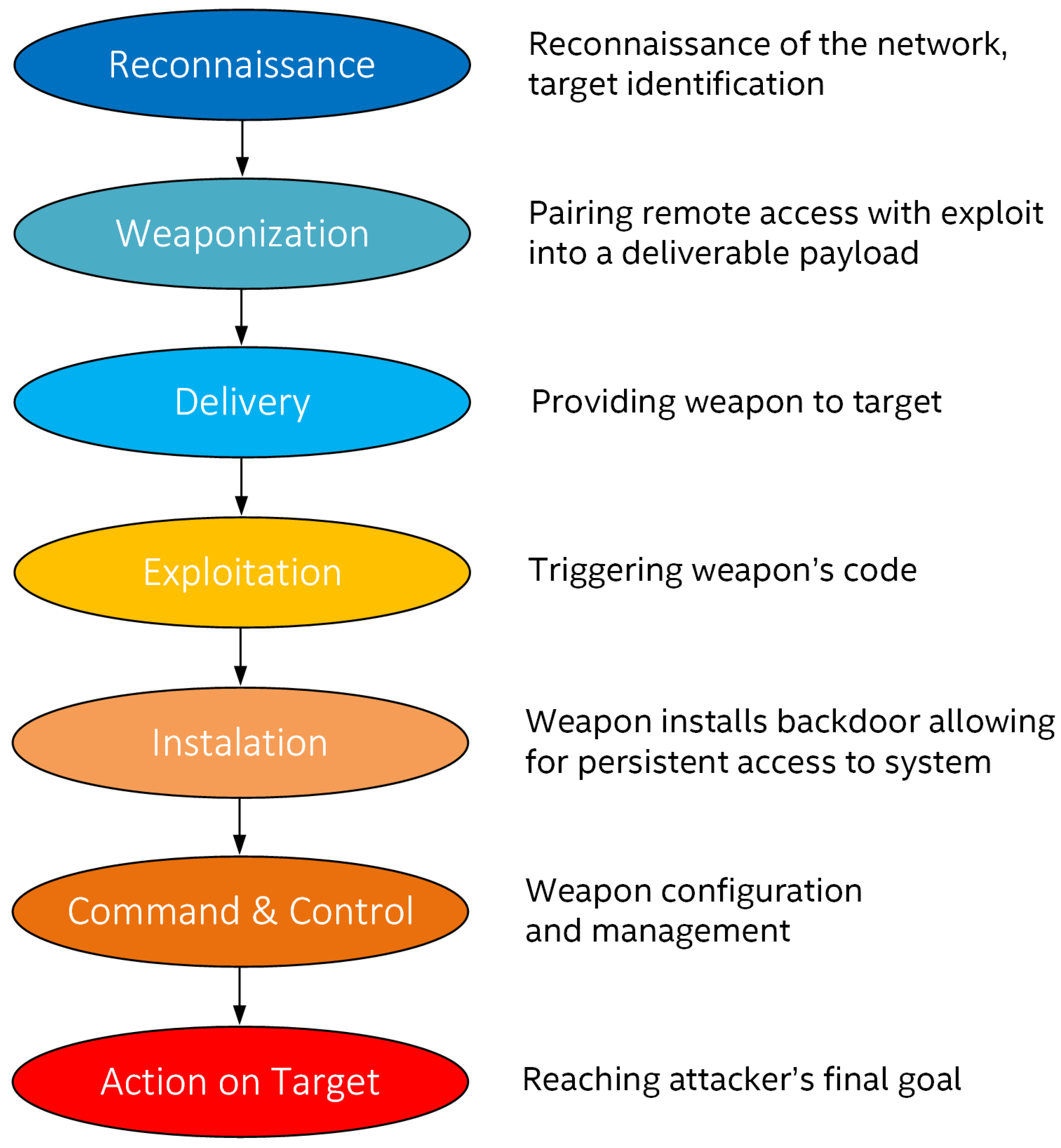
Applied Sciences | Free Full-Text | An Overview of Cyber Threats, Attacks and Countermeasures on the Primary Domains of Smart Cities











![20 Top Cyber Security Tools in 2023 [Most Powerful Tools] 20 Top Cyber Security Tools in 2023 [Most Powerful Tools]](https://intellipaat.com/blog/wp-content/uploads/2021/06/Top-20-Cyber-Security-Tools-Big.png)


